How it works
Instead of managing static API keys, your applications obtain tokens from your identity provider and exchange them for temporary CoreWeave access credentials. These credentials expire after a configurable duration, and your applications refresh them by exchanging new tokens as needed.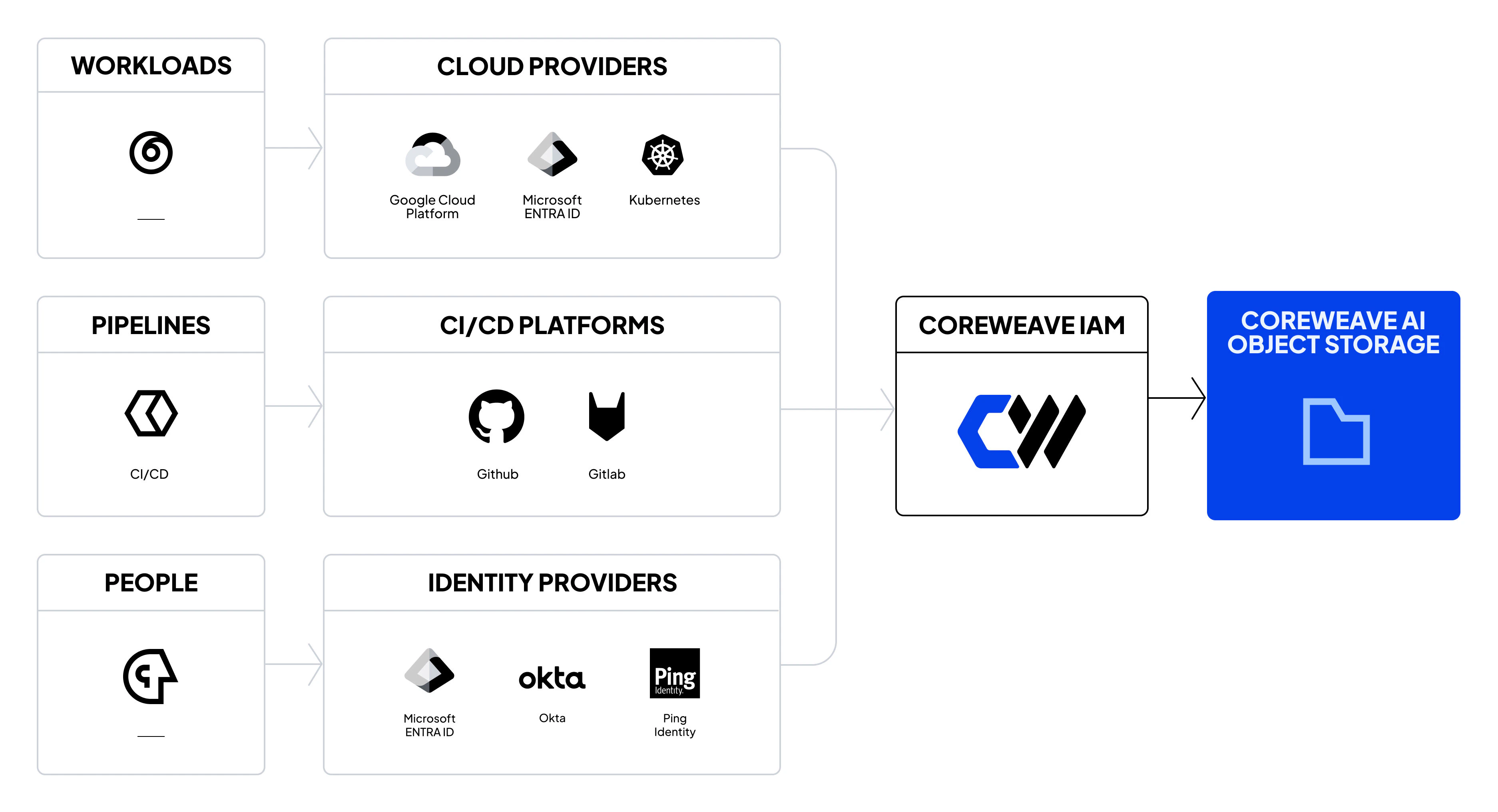
Supported protocols
CoreWeave supports two industry-standard protocols for Workload Identity Federation:- OIDC is the preferred option for cloud-native applications and modern identity providers. It uses JSON Web Tokens (JWT) that integrate easily with programmatic access patterns and that are simpler to debug. Use OIDC if your workloads run on Kubernetes, in cloud environments with OIDC-capable identity providers, or anywhere you can obtain JWTs.
- SAML works well for enterprise environments with existing SAML infrastructure. It uses XML-based assertions that support complex attribute mappings and that integrate with traditional enterprise IdPs.
Connect WIF to access policies
Workload Identity Federation issues temporary credentials tied to a role identity, and you must then create access policies that grant permissions to that role. This step is separate from the authentication process, and you must configure both. Organization access policies are required to grant permissions to WIF roles, while bucket access policies are optional. For most WIF deployments, organization access policies are sufficient. Add bucket access policies only when you have a specific cross-org or bucket-level requirement.Get started
Choose your protocol and follow the end-to-end guide:- Use Workload Identity Federation with OIDC: Recommended for cloud-native workloads.
- Use Workload Identity Federation with SAML: For enterprise SAML environments.

